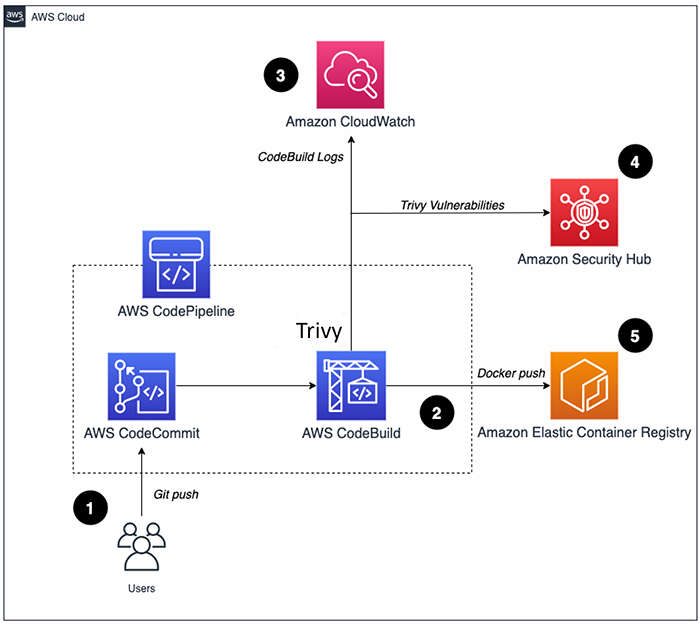
How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog

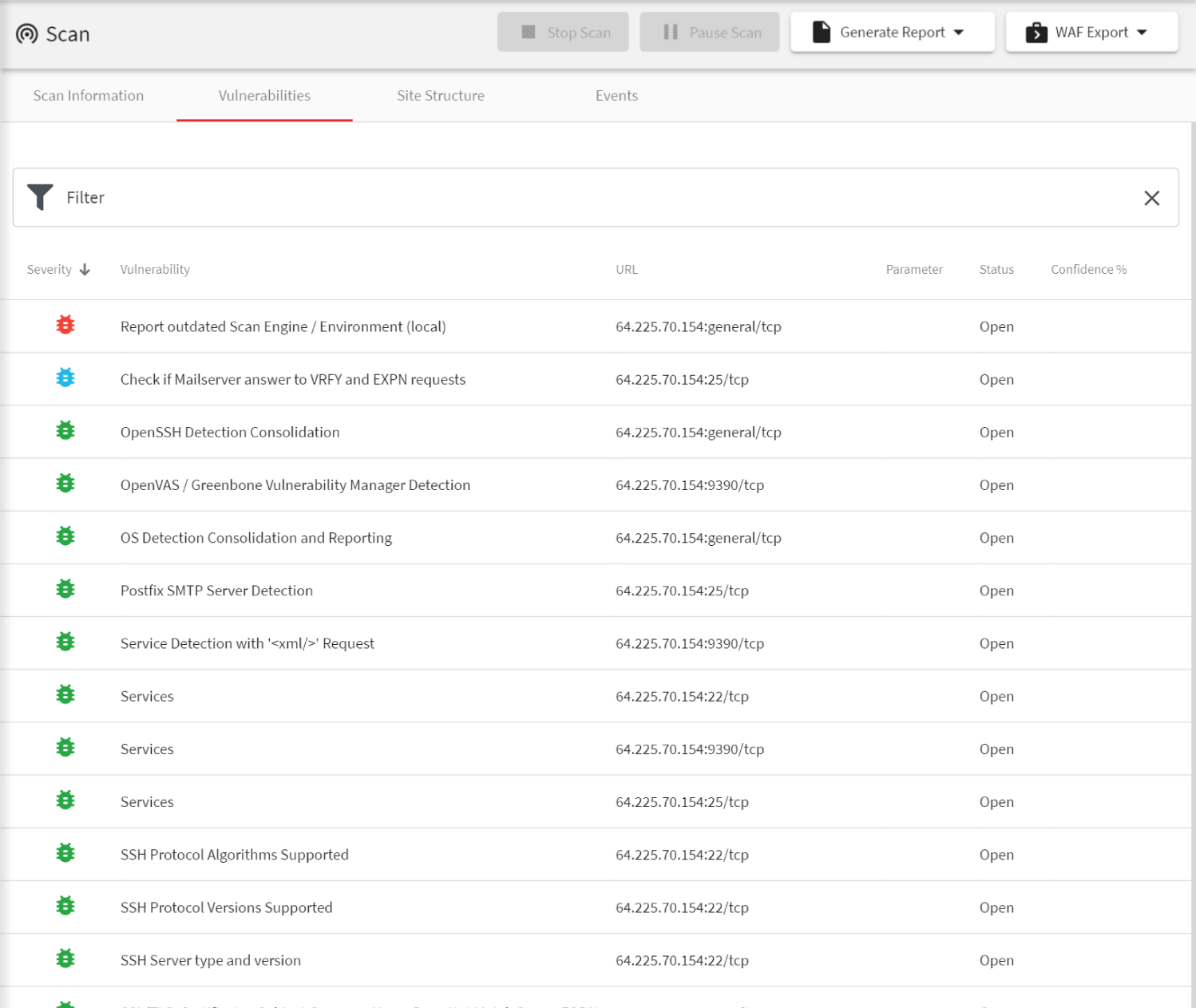
Vulnerability Scanning for Images and Running Containers on Red Hat OpenShift with Vulnerability Advisor | by Chen Nan Li | IBM Cloud | Medium